
Malware
Decrypt the code
What is malware?
Cyber criminals use malware (short for ‘malicious software’) to disrupt computer systems and access confidential information. Malware can easily be installed on your computer or mobile device by clicking a link or opening an email attachment. It can even be hidden inside other files such as software downloads.
How to prevent malware
- Security software: Keep all firewalls and security software regularly updated, consider using antivirus protection and run regular scans on all devices
- Keep devices updated: Install the latest updates for your internet browsers and keep both internet browsers and mobile devices updated to the latest operating systems (OS)
- Trustworthy sources: Only download files and software from trustworthy sources
- Mobile apps: Ensure any mobile apps you download have positive ratings and only use official marketplaces like the Google Store or the App Store
- Emails and texts: Ensure all emails or texts you receive are from legitimate sources before opening any links or attachments, especially if they are pressuring you into taking urgent action
- Passwords: Use complex passwords and multi-factor authentication to make it harder for criminals to access your accounts
- Employee education: Educate employees on how to identify phishing emails and texts and what to do if they receive any
- Disaster recovery plan: Test and rehearse your disaster recovery plan to ensure your business is prepared for an attack.
What to do if you're a victim
- Act immediately: If your computer or device becomes infected by malware take immediate steps to limit the risk of infection and seek professional assistance. Unplug any network cables and de-activate Wi-Fi and Bluetooth connections
- Keep your device on: Do not shut down your device as you may not be able to access it again
- Report: Report the incident immediately to the NCSC1 and Action Fraud2
- Save evidence: Preserve any evidence in coordination with the NCSC, Action Fraud and any other authorities investigating the attack
- Reset credentials: When safe to do so, reset your credentials, including passwords, but ensure not to lock yourself out of systems that are needed for recovery
- Seek advice: Consult the NCSC (National Cyber Security Centre) for advice on how to remove malware3. The No More Ransom Project4 also provides a collection of decryption tools and other anti-malware resources.
Wake up to the reality of malware


5 types of malware
Ransomware
disables system access until a ransom is paid.8
Spyware
secretly monitors devices for user activity data.9
Trojans
malware hidden in desirable software.10
Rootkits
gives hackers remote control over infected devices.11
Keyloggers
monitor keystrokes for sensitive data and credentials.12
Your next steps
Report fraud
To report any fraudulent activity, or attempts, contact Barclays Corporate fraud on 0330 156 0155* or if calling from overseas dial +441606566208.
If you receive a suspicious email, send it as an attachment to internetsecurity@barclays.co.uk and delete the email immediately.
Are you protected?
To keep yourself, and your organisation protected from criminals, ensure you keep up to date with our latest resources and advice.
Fraud and Scam Toolkit
-
1 https://report.ncsc.gov.uk/^
2 https://www.actionfraud.police.uk/^
3 https://www.ncsc.gov.uk/guidance/mitigating-malware-and-ransomware-attacks#stepsifinfected^
4 https://www.nomoreransom.org/en/index.html^
5 https://dataprot.net/articles/most-dangerous-computer-virus/^
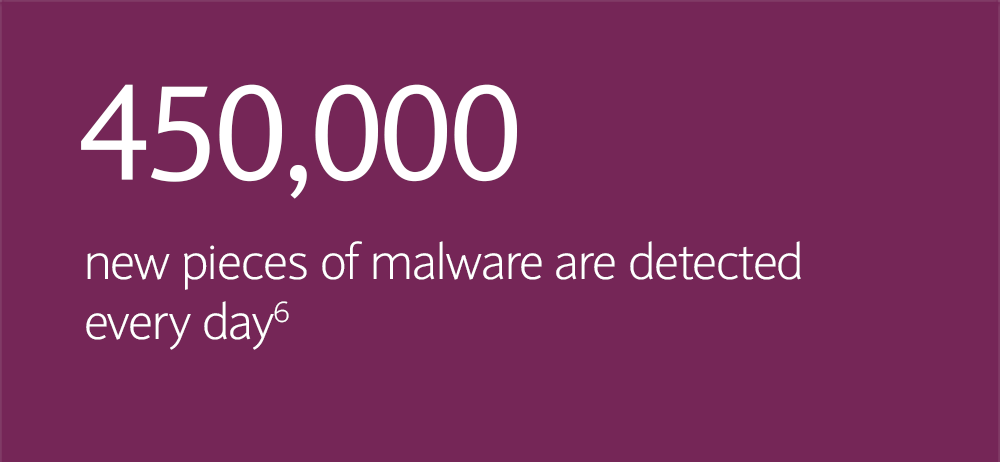
6 https://www.av-test.org/en/statistics/malware/^
7 https://www.comparitech.com/antivirus/malware-statistics-facts/^
8 https://security.berkeley.edu/faq/ransomware/#:~:text=Ransomware%20is%20a%20type%20of,displaying%20an%20on%2Dscreen%20alert^
9 https://www.techtarget.com/searchsecurity/definition/spyware^
10 https://www.zdnet.com/article/trojan-malware-the-hidden-cyber-threat-to-your-pc/^
11 https://us.norton.com/blog/malware/what-is-a-rootkit-and-how-to-stop-them#:~:text=Rootkits%20give%20cybercriminals%20the%20ability,card%20or%20online%20banking%20information^
12 https://home.sophos.com/en-us/security-news/2019/what-is-a-keylogger#:~:text=Keyloggers%20are%20activity%2Dmonitoring%20software,and%20records%20everything%20you%20type^